MAM versus MDM: Data and Device Protections
A lot of organization who rely on Mobile Device Management are starting to understand the risks of Bring Your Own Device.
Watching the Stryker Incident where Intune erased personal devices managed by employers has put the issue in stark contrast.
Mobile Device Management is not enough to secure data.
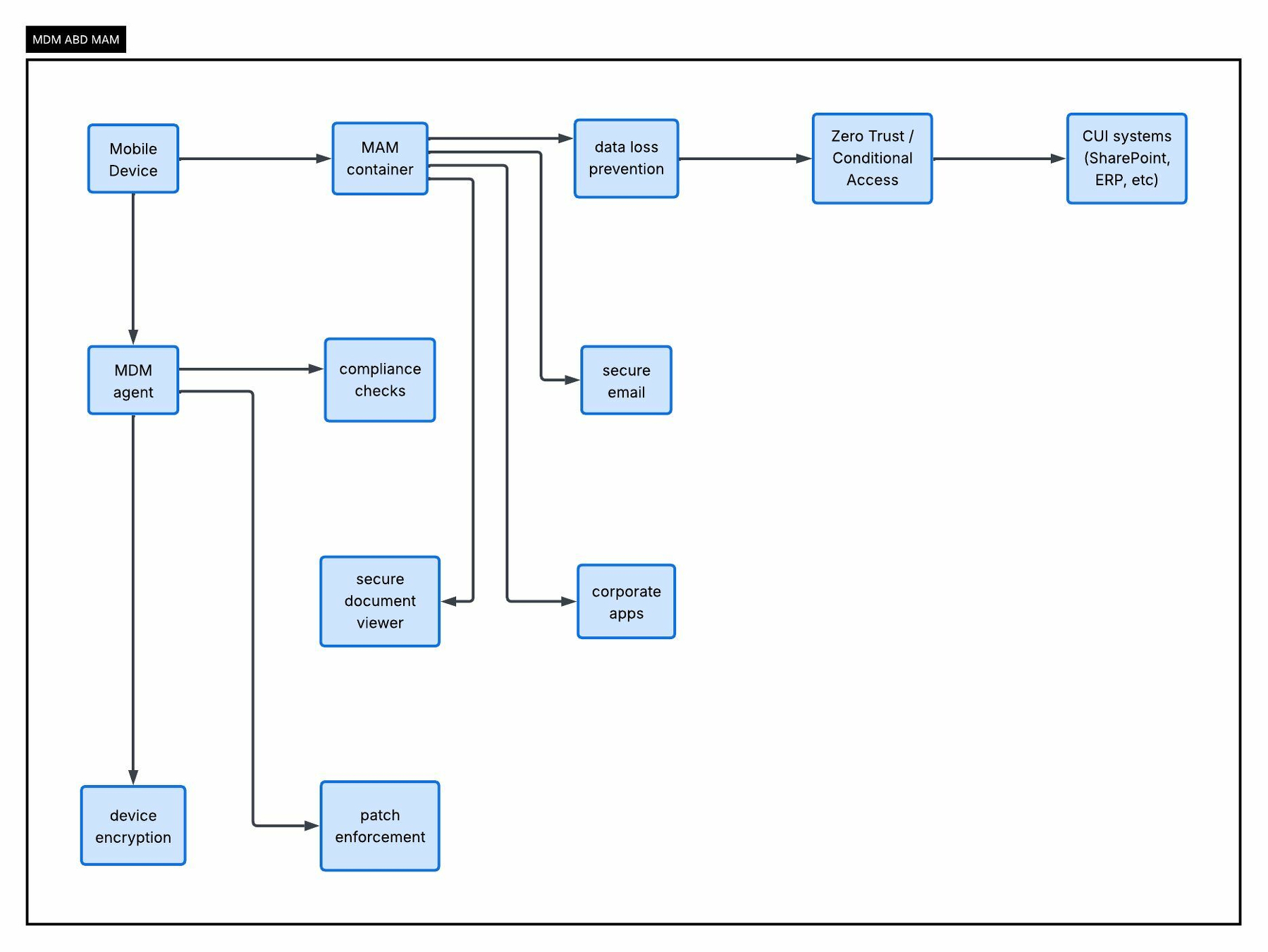
Mobile Device Management (MDM) and Mobile Application Management (MAM) are both enterprise tools used in mobile security controls.
They operate at different layers of data flows. In environments subject to NIST SP 800-171, both MDM and MAM get used to control how mobile devices and apps access sensitive data.
MDM allows administrators to configure, monitor, and secure the entire device, including OS settings, encryption, and remote wipe capabilities.
MAM focuses only on enterprise apps and the business data inside them, using app-level policies like restricting copy/paste or wiping corporate data from an app.
You need to protect the device and the data.
In NIST 800-171 environments, the key requirement for data is cryptography protecting CUI must use FIPS-validated cryptographic modules. When vendors claim “FIPS MAM,” they mean their app container uses FIPS-validated libraries. The MAM isn’t itself “FIPS.”
So with Microsoft Intune MAM App Protection Policies, your container involves App-level MAM policies and SDK/app wrapping. This uses FIPS-validated modules from the OS. When devices run in FIPS mode, Intune apps inherit those modules.
First descope BYOD. If you can’t remember:
MDM = device trust MAM = data protection
You need both.